Have any Project?
Ecommerce
Hydrogen Shopify React Based Dynamic Ecommerce Theme
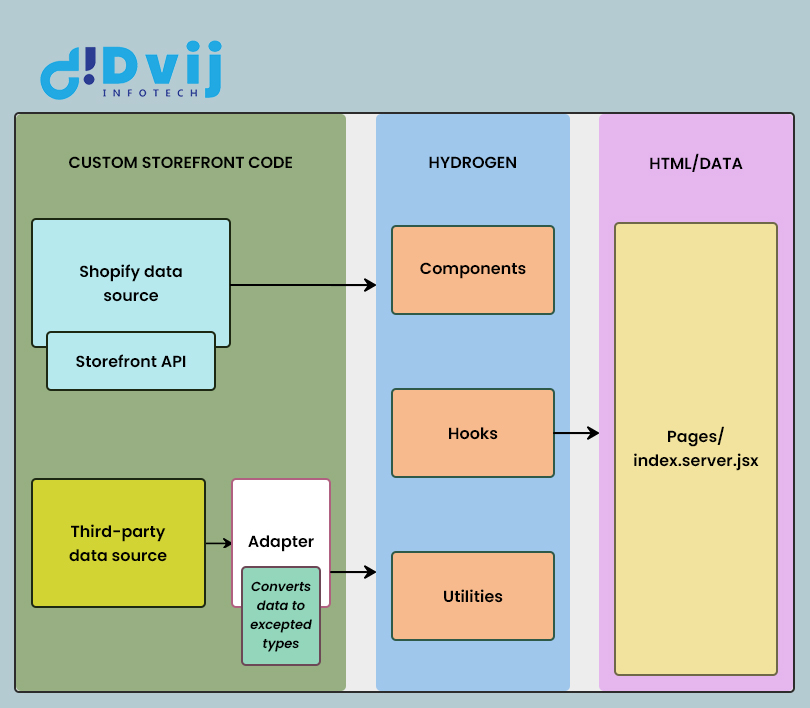
Hydrogen is a front-end web development framework for creating unique Shopify stores. It comes with …